And this trope, this extremely central trope is generally a sticking point in Cyberpunk games. It is to be blunt: Not done particularly well in Tabletop. There are some nice examples in computer games and even board games, but the delivery in tabletop RPGs has been very poor. And I would say that one of the major sticking points is just plain old Player Agency.
In a written story, the characters simply do whatever the author thinks is cool. They have no agency at all. In a computer game, the characters have only a few limited choices, and no real ability to act "outside the box". But in the tabletop RPG, the player can do pretty much anything. And since they are looking at the system actively looking for ways to exploit it and "win" (in character even, in the case of computer hackers), choices that make narrative sense but don't make mechanical sense get passed over. Something "sounding cool" to the author is very much not enough to get the players to use it.
And the results on cyberware choices are obvious and disappointing. No one is willing to trade some of their terribly limited humanity and money away to get awesome looking shark teeth. The results on Matrix rules are more pernicious but still terrible: no one has been able to make a set of computer hacking rules that are anything but hot garbage because it's really hard to do. The Hacker is someone who in character spends most of his time thinking about what are essentially the rules of the game and trying to break the setting through exploits in them. The core realities of the fact that the very nature of computer networks means that they can be expanded.
The problem here is that if it is at all important how many computers are being assigned to a problem, you can add one more. Or a hundred more. You just fucking can. That not only is topography abusable, but topology is as well. If people are able to crack your 256 bit key is cracked too quickly (say: 1 second), it's no problem at all to upgrade to a 65,536 bit key (cracked in over four minutes) or a 4,294,967,296 bit key for that matter (cracked in 195 days). If the enemy hacks through a gateway computer too quickly, just put in another five or 25 gateways. And this works on both ends. If your automated password finder is going to solve the password in 6 hours, why not split the work up to four machines and do it in an hour and a half? Or to 120 machines and get it done in 3 minutes? Both the Security and the Hacker can throw arbitrarily more processing power at any problem.
And it really doesn't help that in many cases, "Team Security" or "Team Hacker" (or both) is going to be played by a street kid who is siphoning power out of a leaky transformer to keep his batteries from running out and sometimes it is going to be played by a multi-trillion dollar global megacorporation that not only has unimaginably titanic resources, but literally produces the computers being used.
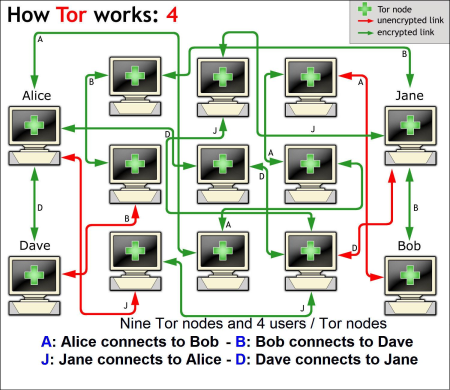
So in the story (or in a card game or computer game), you have this metaphorical wall that represents some access limiting protocol and the Hacker character uses his metaphorical jackhammer to tear a chunk of that wall down so that the character can enter the system. And that's cool imagery. And if you really had to, you could come up with some post hoc explanation that the jackhammer actually represented some sort of trojan that created a temporary backdoor that the character used to log in or some shit. And if you're writing Neuromancer or playing NetRunner, that is sufficient. There is no Player Agency in the computer topology of the world, there's just a description (and possibly a card) for the "wall" and the "hammer". But for a tabletop RPG, it is not. Because the players do not want hostile hackers to jackhammer through their walls, so if they can route traffic through a series of intermediaries to limit the effectiveness of temporary backdoors, they will do that.


How does this work? No one knows!
Which gets us to levels of abstraction. Basically, books and video games and card games work in this medium because they are extremely abstracted. You get some sort of setpiece about how there's a metaphorical wall or a metaphorical guard dog or something and then the Hacker uses some weird metaphor to metaphor themselves past it (or fail). To work in a tabletop role playing game, the stuff needs to be at least as abstracted.
Computer topography can't matter. Computer topology can't matter either. That's going to break peoples' brains, but the sad fact is that a table top role playing game cannot handle worrying about whether a connection is routed through a portable phone in Formosa or not. This may seem like kind of a surprising statement, considering that "I routed the traffic through a portable phone in Formosa" is like the 3rd most likely thing for a Cyberpunk genre hacker to say. But the fact remains that the game can't handle having that statement actually make any difference, because the hacker could jolly well have additional portable phones to route traffic through in Pakistan, Nigeria, and Kentucky and even if that was somehow fair we've already used up too much fucking table time.
The actual game actions need to start and stay very high concept and very abstract, with the details of things being filled in on the fly. The model should probably be Star Trek technobabble. One run you avoid detection by "rerouting traffic through an Icelandic server", and on another run you avoid detection by "spoofing the access ID of an off-duty employee", but it does not matter which you choose because the "Avoid Detection" test is the same regardless. And frankly, the cybernetic upgrades need to be the same. Whether we're playing ICE Cyberspace, Cyberpunk 2020, or Shadowrun, I am simply never going to spend my precious Empathy/Humanity/Essence on having cyberhorns, because horns are kind of stupid and there are much better options to spend that limited resource on (like blades on your arms). The only way "cool concepts" like cyber minotaurs and grafted sharkskin and shit are going to actually happen is to make the upgrades effects based and then let the player go off on their own pseudo-scientific rant about what the hell they did to their body to get those numbers.
-Username17
